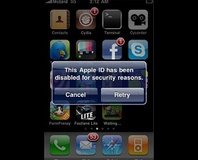
An upgraded version of the iPhone worm which exploited jailbroken handsets is doing the rounds, but this time it's far more malicious.
You may remember the reports of a Dutch cracker who was holding jailbroken iPhones which still had the default SSH password - 'alpine' - to ransom, demanding payments of €5 to secure the device against illegitimate use. Sadly, someone with a far nastier mind has caught on to the idea - interestingly, with the initial reports coming once again from Dutch users.
As reported by Chester Wisniewski at anti-virus vendor Sophos, reports from Dutch ISPs indicate that a suspicious level of traffic was coming from iPhone users - in particular scans aimed at port 22, the TCP port used by the Secure SHell (SSH) service which allows users to log on to a jailbroken iPhone.
Unlike the original attack, this version of the worm is both more sophisticated and more malevolent - joining infected iPhone and iPod Touch handsets to a botnet via a command and control server located in Lithuania and changing the default SSH password to an obscenity to make repairing the damage done that much harder. Before handing control of the iPhone over to the central botnet server, it uploads personal information garnered from the handset - including two-factor authentication SMS mTANs used by online banks - before attempting to scan for other insecure iPhones it can infect. Indeed, the amount of traffic generated is so great that one of the major tell-tales for infection is a drastically reduced battery life when the iPhone is connected to a WiFi network.
So far there appears to be no easy way to remove the worm once infection has taken place, with Wisniewski recommending that users with jailbroken handsets restore the default, locked-down version of the iPhone's operating system via iTunes in order to protect themselves. Tech blog Redmond Pie has alternative advice for those who are not yet infected: simply change the SSH password from the default value, or disable the SSH service altogether once the jailbreak has taken place.
Are you surprised to see a worm of such sophistication hit the iPhone, or has its popularity combined with always-on Internet connectivity made it an obvious target for ne'er-do-wells? Share your thoughts over in the forums.
You may remember the reports of a Dutch cracker who was holding jailbroken iPhones which still had the default SSH password - 'alpine' - to ransom, demanding payments of €5 to secure the device against illegitimate use. Sadly, someone with a far nastier mind has caught on to the idea - interestingly, with the initial reports coming once again from Dutch users.
As reported by Chester Wisniewski at anti-virus vendor Sophos, reports from Dutch ISPs indicate that a suspicious level of traffic was coming from iPhone users - in particular scans aimed at port 22, the TCP port used by the Secure SHell (SSH) service which allows users to log on to a jailbroken iPhone.
Unlike the original attack, this version of the worm is both more sophisticated and more malevolent - joining infected iPhone and iPod Touch handsets to a botnet via a command and control server located in Lithuania and changing the default SSH password to an obscenity to make repairing the damage done that much harder. Before handing control of the iPhone over to the central botnet server, it uploads personal information garnered from the handset - including two-factor authentication SMS mTANs used by online banks - before attempting to scan for other insecure iPhones it can infect. Indeed, the amount of traffic generated is so great that one of the major tell-tales for infection is a drastically reduced battery life when the iPhone is connected to a WiFi network.
So far there appears to be no easy way to remove the worm once infection has taken place, with Wisniewski recommending that users with jailbroken handsets restore the default, locked-down version of the iPhone's operating system via iTunes in order to protect themselves. Tech blog Redmond Pie has alternative advice for those who are not yet infected: simply change the SSH password from the default value, or disable the SSH service altogether once the jailbreak has taken place.
Are you surprised to see a worm of such sophistication hit the iPhone, or has its popularity combined with always-on Internet connectivity made it an obvious target for ne'er-do-wells? Share your thoughts over in the forums.

MSI MPG Velox 100R Chassis Review
October 14 2021 | 15:04








Want to comment? Please log in.