A Dutch cracker has been holding iPhone users on the T-Mobile network to ransom, demanding a payment in order to release his control over their handsets.
According to an article over on Ars Technica, the cracker has been running port scans across T-Mobile Netherlands' IP range in order to find devices with SSH enabled - something which gets turned on when a user 'jailbreaks' their iPhone in order to enable locked features or install software from alternative sources.
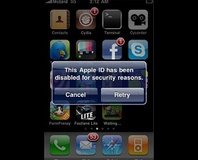
While one of the steps in jailbreaking an iPhone is to change the default SSH password once the service is enabled, many users fail to do so - and it is these insecure devices which the un-named cracker is targeting. Victims of the attack find themselves receiving an SMS from their own handset warning them that their iPhone has "been hacked because it's really insecure!"
A further warning alerts users that the cracker "can access all your files," and advises that the message - and related security hole - won't go away "until your iPhone's secure."
Included in the message is a link to a website, which offers a solution to the issue - pay the cracker €5 via PayPal in order to receive instructions on closing the security hole. The cracker, however, insists that he is doing the user a favour: on the site, he claims that "if you don't pay, it's fine by me," but warns that "the way I got access to your iPhone can be used by thousands of others—they can send text messages from your number (like I did), use it to call or record your calls, and actually whatever they want, even use it for their hacking activities!"
Because the security hole is opened up by deliberately bypassing controls put in place by Apple, it's important that end-users take responsibility back from the company for securing their device. Users of jailbroken iPhones should ensure that they change the root password to something non-trivial, and think about disabling the SSH service when it's no longer required.
Do you believe that the cracker is offering a public service, or is he merely taking advantage of the fact that many iPhone users - even those who have the know-how to jailbreak their handset - are unlikely to think about the security implications of their actions? Share your thoughts over in the forums.
According to an article over on Ars Technica, the cracker has been running port scans across T-Mobile Netherlands' IP range in order to find devices with SSH enabled - something which gets turned on when a user 'jailbreaks' their iPhone in order to enable locked features or install software from alternative sources.
While one of the steps in jailbreaking an iPhone is to change the default SSH password once the service is enabled, many users fail to do so - and it is these insecure devices which the un-named cracker is targeting. Victims of the attack find themselves receiving an SMS from their own handset warning them that their iPhone has "been hacked because it's really insecure!"
A further warning alerts users that the cracker "can access all your files," and advises that the message - and related security hole - won't go away "until your iPhone's secure."
Included in the message is a link to a website, which offers a solution to the issue - pay the cracker €5 via PayPal in order to receive instructions on closing the security hole. The cracker, however, insists that he is doing the user a favour: on the site, he claims that "if you don't pay, it's fine by me," but warns that "the way I got access to your iPhone can be used by thousands of others—they can send text messages from your number (like I did), use it to call or record your calls, and actually whatever they want, even use it for their hacking activities!"
Because the security hole is opened up by deliberately bypassing controls put in place by Apple, it's important that end-users take responsibility back from the company for securing their device. Users of jailbroken iPhones should ensure that they change the root password to something non-trivial, and think about disabling the SSH service when it's no longer required.
Do you believe that the cracker is offering a public service, or is he merely taking advantage of the fact that many iPhone users - even those who have the know-how to jailbreak their handset - are unlikely to think about the security implications of their actions? Share your thoughts over in the forums.

MSI MPG Velox 100R Chassis Review
October 14 2021 | 15:04








Want to comment? Please log in.