A new method for bypassing anti-virus software has been discovered, capable of confusing the vast majority of Windows packages currently available.
Discovered by security firm Matousec - and profiled over on The Register - the discovery makes use of the inability of multi-core systems to effectively track threads running on other processing cores to perform a bait-and-switch attack on the anti-virus software.
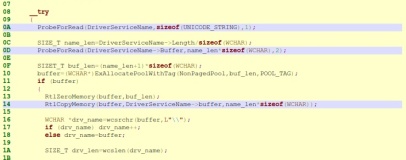
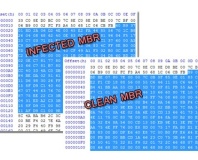
The idea behind the attack is simple to describe but pretty complex to execute: by sending some innocent piece of code to be scanned, it is possible to get the green light from the anti-virus scanner; once validated for execution, there is a very small window during which it is possible to replace the innocuous code with malicious code - which is then executed in its place, without the anti-virus package ever getting a look-in.
According to the team, this technique - which relies on the anti-virus scanner using the System Service Descriptor Table hooks built in to Windows to access certain parts of the operating system's kernel - was effective on "100 percent of the tested products," and provided a list of 34 packages which were known to be vulnerable to the attack.
The list includes many popular free and paid-for packages, including software from Avast!, AVG, BitDefender, Kaspersky, McAfee, Norton, Sophos, and ZoneAlarm. Interestingly, Microsoft's free Security Essentials package is not listed among the vulnerable - although the team say this is due to a lack of time for testing, rather than any evidence of security against the attack.
The team even claim that the attack is effective when executed by a non-privileged account and affects all Windows versions across all architectures, with the only mitigation so far being the complexity of the technique - which requires a large amount of code to be present on the system, making it inefficient for a drive-by attack.
As a proof of concept, the researchers have created an engine for developing exploits called KHOBE, or Kernel HOok Bypassing Engine, which they are using internally for testing. So far the technique is not thought to be in use in-the-wild.
Are you shocked that such a simple-seeming technique as bait-and-switch would work against so many anti-virus packages, or is the technique nothing more than a curiosity that will be too complex for use in-the-wild? Share your thoughts over in the forums.
Discovered by security firm Matousec - and profiled over on The Register - the discovery makes use of the inability of multi-core systems to effectively track threads running on other processing cores to perform a bait-and-switch attack on the anti-virus software.
The idea behind the attack is simple to describe but pretty complex to execute: by sending some innocent piece of code to be scanned, it is possible to get the green light from the anti-virus scanner; once validated for execution, there is a very small window during which it is possible to replace the innocuous code with malicious code - which is then executed in its place, without the anti-virus package ever getting a look-in.
According to the team, this technique - which relies on the anti-virus scanner using the System Service Descriptor Table hooks built in to Windows to access certain parts of the operating system's kernel - was effective on "100 percent of the tested products," and provided a list of 34 packages which were known to be vulnerable to the attack.
The list includes many popular free and paid-for packages, including software from Avast!, AVG, BitDefender, Kaspersky, McAfee, Norton, Sophos, and ZoneAlarm. Interestingly, Microsoft's free Security Essentials package is not listed among the vulnerable - although the team say this is due to a lack of time for testing, rather than any evidence of security against the attack.
The team even claim that the attack is effective when executed by a non-privileged account and affects all Windows versions across all architectures, with the only mitigation so far being the complexity of the technique - which requires a large amount of code to be present on the system, making it inefficient for a drive-by attack.
As a proof of concept, the researchers have created an engine for developing exploits called KHOBE, or Kernel HOok Bypassing Engine, which they are using internally for testing. So far the technique is not thought to be in use in-the-wild.
Are you shocked that such a simple-seeming technique as bait-and-switch would work against so many anti-virus packages, or is the technique nothing more than a curiosity that will be too complex for use in-the-wild? Share your thoughts over in the forums.

MSI MPG Velox 100R Chassis Review
October 14 2021 | 15:04






Want to comment? Please log in.