
Another gift from this years Black Hat DC conference – after the revelation that contactless credit cards aren't such a good idea after all – is the news that cracking the encryption used by the GSM mobile phone standard might be somewhat easier than you may feel comfortable with.
The A5/1 encryption standard used in the EU and the US has been previously considered to be pretty secure, but research conducted by David Hulton of Pico Systems and Steve Muller from CellCrypt shows that the scheme hasn't aged well. The pair used the conference to showcase a device built for £500 which was capable of breaking the A5/1 encryption on an intercepted conversation in under thirty minutes. It's probably worth mentioning the possible conflict of interest at this point: Pico Systems builds very fast custom hardware including the device used in the attack, and CellCrypt... Well, you can probably guess what they do.
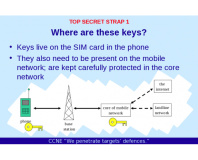
GSM encryption comes in four flavours: A5/0 is no encryption at all, and is the standard for GSM devices shipped to countries the distributors don't like all that much; A5/1 is the fairly robust 'default' encryption implementation used in the EU and the USA; A5/2 is a weakened version of A5/1 offered to countries the distributors have no strong feelings about but which the government may want to keep its eye on; A5/3 is a newcomer to the scene, offering a more robust scheme than A5/1 but currently not implemented for anyone who doesn't work for a three-letter-agency.
A5/2 has been known to be 'broken' for quite some time, with the average time taken to decrypt an intercepted conversation being reported at 15 milliseconds on off-the-shelf PC hardware. A5/1 was, however, always considered secure and the news that interception and decryption of private conversations is within reach of any hacker with a few hundred quid to burn on custom hardware is certain to worry those prone to privacy concerns.
Perhaps the most interesting aspect of the hardware designed by Steve and David is its scalability: the pair claim that by spending $500,000 instead of $1,000 the time taken to decrypt a given message can be dropped to thirty seconds. A worrying thought for those who like their private conversations kept private.
Will you be conducting all your mobile phone conversations in s00per-s3kr1t-c0d3 to circumvent this attack, or is it just one for the ultra-paranoid to worry about? Let us know via the forums.
The A5/1 encryption standard used in the EU and the US has been previously considered to be pretty secure, but research conducted by David Hulton of Pico Systems and Steve Muller from CellCrypt shows that the scheme hasn't aged well. The pair used the conference to showcase a device built for £500 which was capable of breaking the A5/1 encryption on an intercepted conversation in under thirty minutes. It's probably worth mentioning the possible conflict of interest at this point: Pico Systems builds very fast custom hardware including the device used in the attack, and CellCrypt... Well, you can probably guess what they do.
GSM encryption comes in four flavours: A5/0 is no encryption at all, and is the standard for GSM devices shipped to countries the distributors don't like all that much; A5/1 is the fairly robust 'default' encryption implementation used in the EU and the USA; A5/2 is a weakened version of A5/1 offered to countries the distributors have no strong feelings about but which the government may want to keep its eye on; A5/3 is a newcomer to the scene, offering a more robust scheme than A5/1 but currently not implemented for anyone who doesn't work for a three-letter-agency.
A5/2 has been known to be 'broken' for quite some time, with the average time taken to decrypt an intercepted conversation being reported at 15 milliseconds on off-the-shelf PC hardware. A5/1 was, however, always considered secure and the news that interception and decryption of private conversations is within reach of any hacker with a few hundred quid to burn on custom hardware is certain to worry those prone to privacy concerns.
Perhaps the most interesting aspect of the hardware designed by Steve and David is its scalability: the pair claim that by spending $500,000 instead of $1,000 the time taken to decrypt a given message can be dropped to thirty seconds. A worrying thought for those who like their private conversations kept private.
Will you be conducting all your mobile phone conversations in s00per-s3kr1t-c0d3 to circumvent this attack, or is it just one for the ultra-paranoid to worry about? Let us know via the forums.

MSI MPG Velox 100R Chassis Review
October 14 2021 | 15:04






Want to comment? Please log in.