Popular cloud-based password management service LastPass has been hit by the release of a simple yet convincing phishing attack toolkit, but is pushing the blame for its vulnerability onto browser vendors.
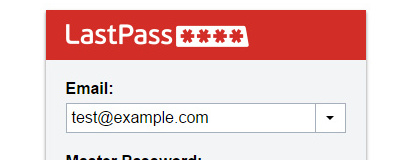
This weekend, security researcher Sean Cassidy released LostPass: an open-source toolkit which allows websites to pop up dialogues near-indistinguishable from those used by password management service LastPass. Using LostPass, Cassidy explained, it was possible for a malicious or compromised website to log the user out of LastPass, prompt for the LastPass username and master password, and even to request a two-factor authentication (2FA) token if enabled on the account. Once provided by the user into the pixel-perfect prompt replicas, the LastPass account could quickly be harvested for all usernames, passwords, and supposedly secure notes stored therein.
The problem, Cassidy explained, lies in how LastPass integrates with the browser. 'A few months ago, LastPass displayed a message on my browser that my session had expired and I needed to log in again. I hadn't used LastPass in a few hours, and hadn't done anything that would have caused me to be logged out. When I went to click the notification, I realized something: it was displaying this in the browser viewport. An attacker could have drawn this notification,' said Cassidy. 'Any malicious website could have drawn that notification. Because LastPass trained users to expect notifications in the browser viewport, they would be none the wiser. The LastPass login screen and two-factor prompt are drawn in the viewport as well.'
The issue was compounded in two ways: a cross-site scripting issue with LastPass would allow any malicious site to genuinely log the user out, making the password reprompt significantly more convicing; and LastPass chose to disable the email verification system when users log in from a new device for accounts which had two-factor authentication enabled, ironically making them more vulnerable to the attack.
Cassidy sent his concerns to LastPass in December, but it initially dismissed LostPass as a simple phishing attack and not of their concern. His publication of the tool, which coincided with him presenting it at a conference this weekend, has the company on the defensive. 'A point that was only briefly raised in Cassidy’s research was the role that the browser itself plays in this attack. LastPass has encouraged Google for years to provide a way to avoid using the browser viewport for notifications,' LastPass explaiend in a statement. 'As a true solution to this threat, Google should release infobars in Chrome that give extensions the capability to do proper notifications outside the DOM. You can see our plea for this back in January 2012 with still no resolution; Issue 453093 is also important as it makes phishing the login window more difficult and may be quicker to release please star these issues to help us raise awareness.'
While LastPass is seemingly blaming Google for the convincing nature of the attack within Chrome - and it's certainly true that Cassidy noted that the attack was trickier to pull off convincingly within Firefox, though far from impossible - the company is also working the resolve the issue internally: the cross-site scripting issue which allowed LostPass to log the user out has been fixed, any attempt to enter the master password on a non-LastPass page will pop up a warning, email verifications are required from all unknown locations or devices even if two-factor authentication is enabled, users are warned if their master password is stored as a password for a third-party site, and the company is working on bypassing the viewport and serving up notifications in a new way on future releases.
The flaw is publicised as the National Fraud Intelligence Bureau has issued a statement claiming that phishing attacks accounted for £174.4 million in losses for 2015, with the number of victims rising 21 per cent year-on-year.
This weekend, security researcher Sean Cassidy released LostPass: an open-source toolkit which allows websites to pop up dialogues near-indistinguishable from those used by password management service LastPass. Using LostPass, Cassidy explained, it was possible for a malicious or compromised website to log the user out of LastPass, prompt for the LastPass username and master password, and even to request a two-factor authentication (2FA) token if enabled on the account. Once provided by the user into the pixel-perfect prompt replicas, the LastPass account could quickly be harvested for all usernames, passwords, and supposedly secure notes stored therein.
The problem, Cassidy explained, lies in how LastPass integrates with the browser. 'A few months ago, LastPass displayed a message on my browser that my session had expired and I needed to log in again. I hadn't used LastPass in a few hours, and hadn't done anything that would have caused me to be logged out. When I went to click the notification, I realized something: it was displaying this in the browser viewport. An attacker could have drawn this notification,' said Cassidy. 'Any malicious website could have drawn that notification. Because LastPass trained users to expect notifications in the browser viewport, they would be none the wiser. The LastPass login screen and two-factor prompt are drawn in the viewport as well.'
The issue was compounded in two ways: a cross-site scripting issue with LastPass would allow any malicious site to genuinely log the user out, making the password reprompt significantly more convicing; and LastPass chose to disable the email verification system when users log in from a new device for accounts which had two-factor authentication enabled, ironically making them more vulnerable to the attack.
Cassidy sent his concerns to LastPass in December, but it initially dismissed LostPass as a simple phishing attack and not of their concern. His publication of the tool, which coincided with him presenting it at a conference this weekend, has the company on the defensive. 'A point that was only briefly raised in Cassidy’s research was the role that the browser itself plays in this attack. LastPass has encouraged Google for years to provide a way to avoid using the browser viewport for notifications,' LastPass explaiend in a statement. 'As a true solution to this threat, Google should release infobars in Chrome that give extensions the capability to do proper notifications outside the DOM. You can see our plea for this back in January 2012 with still no resolution; Issue 453093 is also important as it makes phishing the login window more difficult and may be quicker to release please star these issues to help us raise awareness.'
While LastPass is seemingly blaming Google for the convincing nature of the attack within Chrome - and it's certainly true that Cassidy noted that the attack was trickier to pull off convincingly within Firefox, though far from impossible - the company is also working the resolve the issue internally: the cross-site scripting issue which allowed LostPass to log the user out has been fixed, any attempt to enter the master password on a non-LastPass page will pop up a warning, email verifications are required from all unknown locations or devices even if two-factor authentication is enabled, users are warned if their master password is stored as a password for a third-party site, and the company is working on bypassing the viewport and serving up notifications in a new way on future releases.
The flaw is publicised as the National Fraud Intelligence Bureau has issued a statement claiming that phishing attacks accounted for £174.4 million in losses for 2015, with the number of victims rising 21 per cent year-on-year.

MSI MPG Velox 100R Chassis Review
October 14 2021 | 15:04








Want to comment? Please log in.