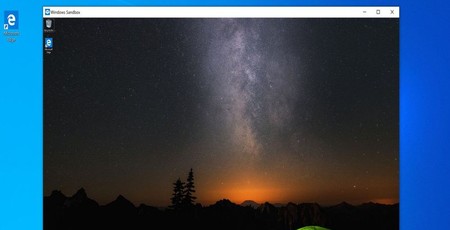
Microsoft has officially announced Windows Sandbox, formerly known as InPrivate Desktop, through which users can run untrusted executables in relative isolation.
InPrivate Desktop was first leaked back in August as an upcoming feature of Microsoft's Windows 10 operating system. Named for the private browsing mode of the company's Edge web browser, InPrivate Desktop was claimed to add an integrated, high-performance virtual machine (VM) to Windows 10 which can be fired up to run a single untrusted application and automatically 'recycled' when the app is closed, insulating the host operating system from any ill effects.
While Microsoft didn't comment on the leak at the time, it has now made the feature official - though it's now known as Windows Sandbox. In a community post, Microsoft's Hari Pulapaka details the features of Windows Sandbox: 'How many times have you downloaded an executable file, but were afraid to run it? Have you ever been in a situation which required a clean installation of Windows, but didn’t want to set up a virtual machine?
'At Microsoft we regularly encounter these situations, so we developed Windows Sandbox: an isolated, temporary, desktop environment where you can run untrusted software without the fear of lasting impact to your PC. Any software installed in Windows Sandbox stays only in the sandbox and cannot affect your host. Once Windows Sandbox is closed, all the software with all its files and state are permanently deleted.'
According to Pulapaka, Windows Sandbox has a range of benefits compared to rolling your own virtual machine: It's built in to Windows 10, albeit exclusively in the Pro and Enterprise flavours; it automatically resets itself upon application close and is wholly disposable; it's secure, using hardware virtualisation extensions for kernel isolation which means it's only compatible with systems that have virtualisation extensions in their CPU and enabled in the BIOS; and it's efficient, using an integrated kernel scheduler, smart memory management, and a virtual GPU implementation.
The feature is available to install now through the Windows Features control panel in Windows 10 Pro or Enterprise build 18305 or later, though its security is as-yet unproven. More details are available in Pulapaka's announcement.

MSI MPG Velox 100R Chassis Review
October 14 2021 | 15:04








Want to comment? Please log in.