The still-popular cryptographic hash function SHA-1 has been officially broken, two decades after it was introduced, by researchers working at Google and Centrum Wiskunde & Informatica (CWI) Amsterdam.
Designed by the US National Security Agency and adopted as a formal US Federal Information Processing Standard by the National Institute of Standards and Technology (NIST), SHA-1 (Secure Hash Algorithm 1) is a one-way hash function: given data, it spits out a fixed-length message digest which becomes invalid if the data is modified in any way. It's used for everything from checking that downloaded data hasn't been corrupted and ensuring that files uploaded to shared hosting have unique filenames to validating passwords against a database without having to store the password in plain text, digital signing, and the TLS cryptography standard.
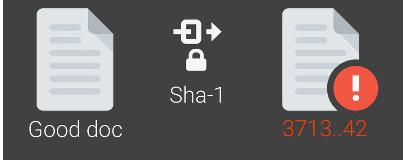
Sadly, it has also been proven flawed: A team of researchers from Google and CWI Amsterdam have been able to create the first practical SHA-1 collision, creating two valid PDF files which have different content but produce the same SHA-1 hash in an attack the team has dubbed SHAttered.
In SHA-1's defence, while the successful collision attack proves that the algorithm is unsuitable for top-security work, it took some considerable effort on Google's part: To find the collision, the company needed to produce nine quintillion SHA-1 hashes, which took a total 6,500 years of CPU time and a further 110 years of GPU time to complete. The company isn't saying how it did it just yet, though: following the Project Zero responsible disclosure policy, Google is keeping the code used to generate the PDFs private for 90 days to allow vendors time to deprecate the SHA-1 algorithm.
Although SHA-1 was officially deprecated by NIST in 2011, it is still in widespread use today. Google's own browser, Chrome, has been phasing out SHA-1 since 2014, while rival browser Firefox disables SHA-1 from version 52 onwards. Google has already added detection of SHAttered attacks to its Gmail and GSuite platforms, while a tool to test files for evidence of SHAttered attack can be found on the official website.
Developers and system administrators currently using SHA-1 in production are advised to move to an alternative algorithm, such as SHA-256 or SHA-3.
Designed by the US National Security Agency and adopted as a formal US Federal Information Processing Standard by the National Institute of Standards and Technology (NIST), SHA-1 (Secure Hash Algorithm 1) is a one-way hash function: given data, it spits out a fixed-length message digest which becomes invalid if the data is modified in any way. It's used for everything from checking that downloaded data hasn't been corrupted and ensuring that files uploaded to shared hosting have unique filenames to validating passwords against a database without having to store the password in plain text, digital signing, and the TLS cryptography standard.
Sadly, it has also been proven flawed: A team of researchers from Google and CWI Amsterdam have been able to create the first practical SHA-1 collision, creating two valid PDF files which have different content but produce the same SHA-1 hash in an attack the team has dubbed SHAttered.
In SHA-1's defence, while the successful collision attack proves that the algorithm is unsuitable for top-security work, it took some considerable effort on Google's part: To find the collision, the company needed to produce nine quintillion SHA-1 hashes, which took a total 6,500 years of CPU time and a further 110 years of GPU time to complete. The company isn't saying how it did it just yet, though: following the Project Zero responsible disclosure policy, Google is keeping the code used to generate the PDFs private for 90 days to allow vendors time to deprecate the SHA-1 algorithm.
Although SHA-1 was officially deprecated by NIST in 2011, it is still in widespread use today. Google's own browser, Chrome, has been phasing out SHA-1 since 2014, while rival browser Firefox disables SHA-1 from version 52 onwards. Google has already added detection of SHAttered attacks to its Gmail and GSuite platforms, while a tool to test files for evidence of SHAttered attack can be found on the official website.
Developers and system administrators currently using SHA-1 in production are advised to move to an alternative algorithm, such as SHA-256 or SHA-3.

MSI MPG Velox 100R Chassis Review
October 14 2021 | 15:04








Want to comment? Please log in.