Thunderbolt vulnerability exposed by University researchers
May 12, 2020 | 13:00
Companies: #eindhoven-university-of-technology
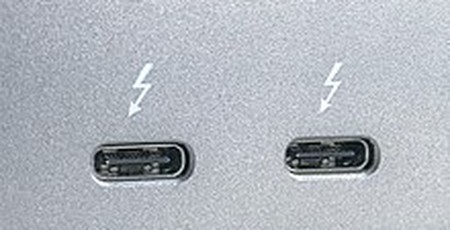
A new vulnerability has been found in the Thunderbolt port and there's no way of fixing it.
A team of researchers at Eindhoven University of Technology has found that it's possible to unlock any PC running Windows or Linux in less than 5 minutes via the exploit. The somewhat reassuring thing about this? The attacker needs to have physical access to do this so there's a fairly obvious way of stopping this from occurring.
The method known as Thunderspy utilises a feature built into the Thunderbolt firmware known as Security Level. It disallows access to untrusted devices and can even switch off the Thunderbolt port, switching it to a simple USB or display output. The problem with the exploit is that researchers have found a way to alter the firmware setting of the control chip in a way that it basically does the opposite effect.
It's a method that can be done without any trace and without the operating system acknowledging that any changes were committed. It uses an SPI (Serial Peripheral Interface) programmer with a SOP8 clip that connect the pins of the programmer device to the Thunderbolt 3 controller, leaving the attacker able to easily run a script from there.
Certain devices are able to withstand the attack thanks to Intel implementing Kernal Direct Memory Access Protection on some hardware but the feature isn't available on PCs manufactured before 2019 and not all PC manufacturers have utilised it since, so there are still plenty of devices that are vulnerable.
Fortunately, of course, the flaw does require the attacker to physically access the desktop or laptop system. It also requires around $400 worth of hardware alongside the basic components, so it takes a certain amount of planning and determination. This isn't going to happen often at all and allowing physical access to anyone is always going to theoretically be a risk when dealing with sensitive data. However, the fact it exists is still an issue for security-conscious individuals and companies.
As the Thunderspy site explains, it's also uncertain whether this issue will transfer to USB 4 too as the format is based on Thunderbolt 3. For now, the research team recommends caution until the vulnerability has been fully addressed. It also refers to other issues with the technology.
Like a lot of unusual vulnerabilities such as last week's Air-ViBeR, this is more of an interesting concept than something you need to genuinely worry about as a consumer, but it's fascinating to see what can be accomplished, as well as what's presumably being missed out during development.

MSI MPG Velox 100R Chassis Review
October 14 2021 | 15:04








Want to comment? Please log in.