Reports have begun circling that Intel is in the process of patching yet more vulnerabilities in its processors, dubbed Spectre Next Generation or Spectre-NG.
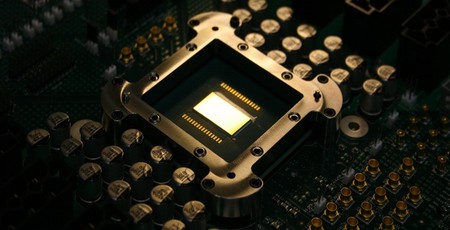
The cross-vendor Spectre and largely Intel-specific Meltdown vulnerabilities caused quite a stir when announced back in January this year. Stemming from speculative execution, a performance-boosting technology found in the overwhelming majority of modern mainstream processors, the vulnerabilities were notable for existing directly in the silicon itself - meaning that patching it out properly requires replacing the chip. Since its public release, microcode updates have become available alongside software mitigations - though not without side-effects - and development work on silicon safe from both flaws is under way.
Sadly, the story doesn't seem likely to end there. German technology outlet C't has published a report this week claiming to have confirmed that Intel is investigating eight new hardware-related vulnerabilities in the Spectre family, to which it has assigned the codename Spectre Next Generation or Spectre-NG.
Details of these flaws are, the site reports, being kept under close wraps - a distinct departure from the handling of Meltdown, which was leaked to the public before a scheduled formal announcement. The site's sources claim that the first Spectre-NG patch from Intel is due to launch this month, with an additional patch in August; whether the Spectre-NG flaws affect AMD, which was immune to Meltdown but not to Spectre, is not yet known.
Intel is said to classify four of the Spectre-NG vulnerabilities as high risk and the remaining four as moderate risk, but researchers for C't claim that one of the eight vulnerabilities 'simplifies attacks across system boundaries to such an extent that we estimate the threat potential to be significantly higher than with Spectre' - including the potential for code running in a sandbox or virtual machine to directly attack the host.
Intel has not commented on the site's claims.
UPDATE 07/05/2018: Intel has issued a brief statement on the matter, which neither confirms nor denies the existence of the vulnerabilities nor the planned release of patches for same. The statement reads: 'Protecting our customers’ data and ensuring the security of our products are critical priorities for us. We routinely work closely with customers, partners, other chipmakers and researchers to understand and mitigate any issues that are identified, and part of this process involves reserving blocks of CVE numbers. We believe strongly in the value of coordinated disclosure and will share additional details on any potential issues as we finalize mitigations. As a best practice, we continue to encourage everyone to keep their systems up-to-date.'

MSI MPG Velox 100R Chassis Review
October 14 2021 | 15:04








Want to comment? Please log in.