Intel warns of serious Management Engine vulnerabilities
November 21, 2017 | 10:54
Companies: #eff #electronic-frontier-foundation #intel
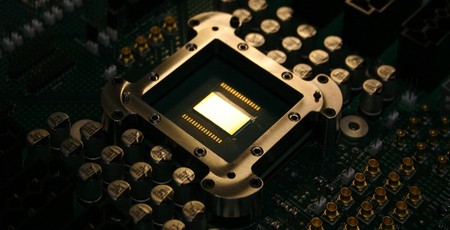
Intel has warned of serious flaws in the Intel Management Engine (IME), a secondary Minix-based computer built into all recent Intel platforms, which allows for the execution of arbitrary code completely outside the visibility of the host operating system.
Designed to provide everything from an active low-power standby mode to security functionality, the Intel Management Engine (IME) is effectively a secondary computer which runs alongside the main processor and operating system. Sharing no direct memory links, the Minix-based IME is capable of running any code without the host operating system's interference - hence its use to drive Intel's Active Management Technology (AMT), a remote maintenance platform targeting enterprise users managing scores of client systems.
Since the IME launched in 2008, however, privacy and security advocates have been campaigning against it. An article by the Electronic Frontier Foundation (EFF) from May this year described it as a 'security hazard', and now Intel has proven the group right by issuing a security advisory warning that the IME can be exploited to run arbitrary code and take full control over a target system - regardless of said system's operating system or any security measures in place.
'In response to issues identified by external researchers, Intel has performed an in-depth comprehensive security review of our Intel Management Engine (ME), Intel Server Platform Services (SPS), and Intel Trusted Execution Engine (TXE) with the objective of enhancing firmware resilience,' the company explains in its announcement of the flaws. 'As a result, Intel has identified security vulnerabilities that could potentially place impacted platforms at risk.
'Based on the items identified through the comprehensive security review, an attacker could gain unauthorized access to platform, Intel ME feature, and third party secrets protected by the Intel Management Engine (ME), Intel Server Platform Service (SPS), or Intel Trusted Execution Engine (TXE). This includes scenarios where a successful attacker could: Impersonate the ME/SPS/TXE, thereby impacting local security feature attestation validity; Load and execute arbitrary code outside the visibility of the user and operating system; Cause a system crash or system instability.'
In short: It's a serious flaw, and one which affects almost every platform Intel has released in recent years. Any machine running a 6th, 7th, or 8th generation Intel Core processor, Intel Xeon E3-1200 v5 or v6, Xeon Processor Scalable, Xeon Processor W, Atom C3000, Apollo Lake-based Atom or Pentium, or a Celeron N or J series processor is vulnerable to attack, the company has confirmed.
Although Intel has patched the vulnerabilities, the fixes are not yet available to end-users. Instead, Intel has issued a microcode update to vendors, who must now integrate that update into a firmware update for their systems - a process which could take considerable time to complete and has the potential to leave older systems without access to the patch.
Although Intel's patch will resolve the issue, the company has still not responded to calls to allow users to turn the Intel Management Engine off, nor has it provided anyone with access to the source code for an external security audit.
UPDATE:
Intel has released a vulnerability testing tool for Windows 10 and Linux which can detect the presence of a vulnerable Management Engine. Those finding their systems are vulnerable, however, still have no choice but to wait for the release of a patch from their vendor.

MSI MPG Velox 100R Chassis Review
October 14 2021 | 15:04








Want to comment? Please log in.