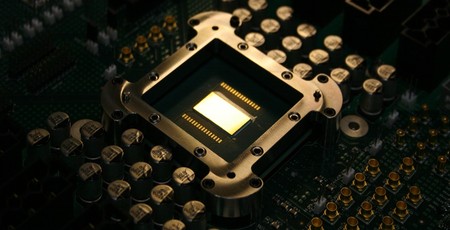
A serious hardware security flaw in Intel processors is being actively patched in software, but with warnings that its implementation can result in a performance loss for affected workloads of between five and 30 percent depending.
In the second major security gaffe to hit Intel in the past three months, following the discovery of a security vulnerability in the Intel Management Engine (IME) in November, details surrounding the flaw are presently being held back until fixes can be developed and released. What is known, however, is that the issue stems from optimisations introduced to improve processor performance and allow supposedly-secure kernel-level memory to be accessed by user-level processes as trivially as running JavaScript in a web browser.
A blog post published on January 1st brought public attention to the issue, based largely upon messages to the Linux Kernel Mailing List (LKML) discussing patches for a sweeping change to the way the Linux kernel operates, previously worked upon under the codename KAISER and now known as Page Table Isolation (PTI), while Microsoft has been working on similar changes. The release of a Linux kernel with the kernel page table isolation patches merged has confirmed that processors are being marked as 'insecure' and worked around, with a corresponding impact in performance of affected workloads - meaning the flaw is real and is actively exploitable until the patches can be rolled out to users.
For Intel, the security flaw is a major headache: The issue appears to affect every Intel part around, from top-end server chips - where the security impact is the greatest but where the performance loss will also be hardest felt - through to embedded parts. For AMD, the news could be a welcome bonus: While the current release of the Linux patch implements the isolation feature on all x86 and x86-64 processors regardless of vendor, AMD chips have been confirmed as not vulnerable to the issue with a patch being released to disable the workaround and thus restore performance on all AMD processors.
Thus far, Intel has not publicly commented in the issue.

MSI MPG Velox 100R Chassis Review
October 14 2021 | 15:04









Want to comment? Please log in.